The Sentinel intercontinental ballistic missile program[2] triggered a cost breach indicating an 81% increase in unit cost.[1] Three structural gaps in cost accounting, baseline comparability, and computation reproducibility prevented stakeholders from detecting or contesting this breach until too late. A machine-readable, reproducible cost framework—UC-BCK—closes these gaps.
In July 2024, the Department of Defense announced a unit-cost breach[1] in the Sentinel program. The program's per-unit cost grew from an original baseline of $118 million to $214 million—an 81.3% increase.[2] This exceeded the 50% Nunn-McCurdy statutory threshold for a critical breach. Total program cost reached $140.9 billion.[3]
In February 2026, the Air Force restructured the program,[2] introducing 450 new modular silos and approximately 5,000 miles of fiber-optic infrastructure.[4] A prototype broke ground at Promontory, Utah. These changes reset baseline computations, but without UC-BCK, the same gaps persist.
10 U.S.C. § 4371[5] establishes two metrics for breach detection:
The FY 2006 NDAA[6] introduced dual-baseline tracking, requiring programs to report growth against both the current baseline and the original Milestone B baseline—closing the "rebaselining loophole" that previously let programs reset their breach counters:
| Classification | vs. Current Baseline | vs. Original Baseline | Consequence |
|---|---|---|---|
| Significant | ≥ 15% | ≥ 30% | Service Secretary notifies Congress within 45 days |
| Critical | ≥ 25% | ≥ 50% | Secretary of Defense certification required; potential termination |
| Sentinel Actual | — | 81% | CRITICAL BREACH |
Source: 10 U.S.C. § 4371;[5] DAU Statutory Program Breach Definitions.[7]
Upon a critical breach, 10 U.S.C. § 4376[8] requires the Secretary of Defense to certify five things within 60 days—or the program is terminated:
For Sentinel, USD(A&S) certified the program on all five criteria in July 2024.[1] Milestone B approval was rescinded, requiring restructuring and a new milestone review.
Nunn-McCurdy breaches are surfaced through four primary channels:
All four channels are essential but disconnected. SARs arrive quarterly but may lag actual cost trending. DAVE and CADE require CAC access. UCRs are often contested because the baseline they reference is ambiguous.
Sentinel's breach was not "impossible to foresee"—it was impossible to compute reproducibly until seven months after cost overruns had metastasized. Three structural gaps explain why:
What is a "unit" in Sentinel? The CRS has documented recurring unit definition disputes[13] across historical programs:
Without a locked, machine-readable definition approved by the milestone authority, contractors and programs can redefine the unit retroactively, masking breaches or shifting them to different metrics.
A 2005 GAO audit found that programmatic adjustments masked approximately 50% of Nunn-McCurdy breaches[17] between 2001 and 2003. GAO identified 25 programs with cost growth, but only 17 were formally reported as breaches.
Without a frozen, auditable baseline-to-current crosswalk, breaches can be masked indefinitely.
Even when PAUC and APUC figures are published, no independent party can reproduce them from source data. The calculation depends on:
Contractors submit cost data to DAVE,[10] but those data are optimized for narrative rather than reproducible computation. CADE holds more detailed FlexFile repositories,[12] but the mapping from FlexFile categories to Nunn-McCurdy unit cost is manual, undocumented, and varies by program.
Cost growth in complex acquisition follows a feedback loop. Cooper (1993) documented how rework cycles in development projects compound through iterative discovery and correction.[18] Ford and Sterman (2003) modeled how rework concealment in concurrent development creates cascading cost surprises.[19] Gansler (1999) termed this "funding migration," where rising O&S costs for aging systems consume modernization budgets, forcing quantity reductions on new programs.[20]
The F-22 program initially planned 750 aircraft.[21] Successive budget cuts triggered quantity reductions:
Total RDT&E reached approximately $24.3 billion,[22] making per-aircraft development cost unsustainably high.
The DDG-1000 was originally planned for 32 ships.[23] Cost overruns led to successive reductions:
GAO documented cost growth driving down quantity,[24] yet each reduction was justified as a "force structure trade" rather than programmatic failure.
The JDAM achieved a 25% unit cost reduction and procured more than double the originally planned quantity.[16] Unadjusted total cost growth substantially overstated the program's cost management problems, because quantity increases drove total spending up even as per-unit costs fell. Both directions matter—adjustments can hide bad news or obscure good news.
In January 2024, the Air Force notified Congress of the breach.[3] By July 2024, the Department formally announced the results: unit cost had grown 81%.[1]
The 81% figure refers to PAUC growth ($118M → $214M per unit) and is valid as a ratio. As of March 2026, no new cost estimate reflecting the February 2026 restructure has been published.[2]
The Department's root cause analysis determined that approximately 80% of cost growth originated in the Command & Launch segment[1]—ground infrastructure, real estate, and fiber-optic communications rather than the missile airframe.
However—and this is critical—no public segment-level dollar breakdowns exist. Only the aggregate 80% figure is acknowledged. This opacity is precisely the computational non-reproducibility that Gap CS2 describes.
These changes reset the baseline, but without UC-BCK, they also reset the reproducibility clock.
MC1 (Unit Definition): Sentinel was costed as a "missile system." Requirements crept in for integrated command, control, communications, and cyber-hardening. The program used baseline adjustments to avoid reporting breaches, until the 81% threshold could no longer be suppressed.
CS1 (Baseline Masking): Adjustments for "threat environment changes" and "STRATCOMM integration" were justified in narrative, but no formal crosswalk documented "original scope" vs. "new scope."
CS2 (Non-Reproducibility): The 81% figure appeared in press releases and SARs, but the underlying calculation was not published. Congress and GAO had to accept the DoD's announcement or fund an audit.
Two systems hold the raw data needed: DAVE[10] and CADE.[12]
DAVE is the DoD's authoritative system for acquisition program data,[10] API-oriented[11] but access-restricted. It presents aggregated views optimized for narrative rather than reproducible computation.
CADE[12] houses FlexFile repositories in the CSDR format,[27] historical baselines, and cross-organizational access for audit.
FlexFile[28] is defined by DI-FNCL-82162.[29] Programs submit cost data in seven groups:
CSDR requires quarterly submission.[30] However, the mapping from FlexFile categories to Nunn-McCurdy "unit" definitions is not standardized; each program interprets the mapping differently.
The critical gap is not data availability—it is data integration and reproducibility. DAVE and CADE are disconnected. No party can independently reproduce a breach computation from first principles.
What is missing is the governance and architecture for making that data reproducible and contestable. UC-BCK bridges that gap.
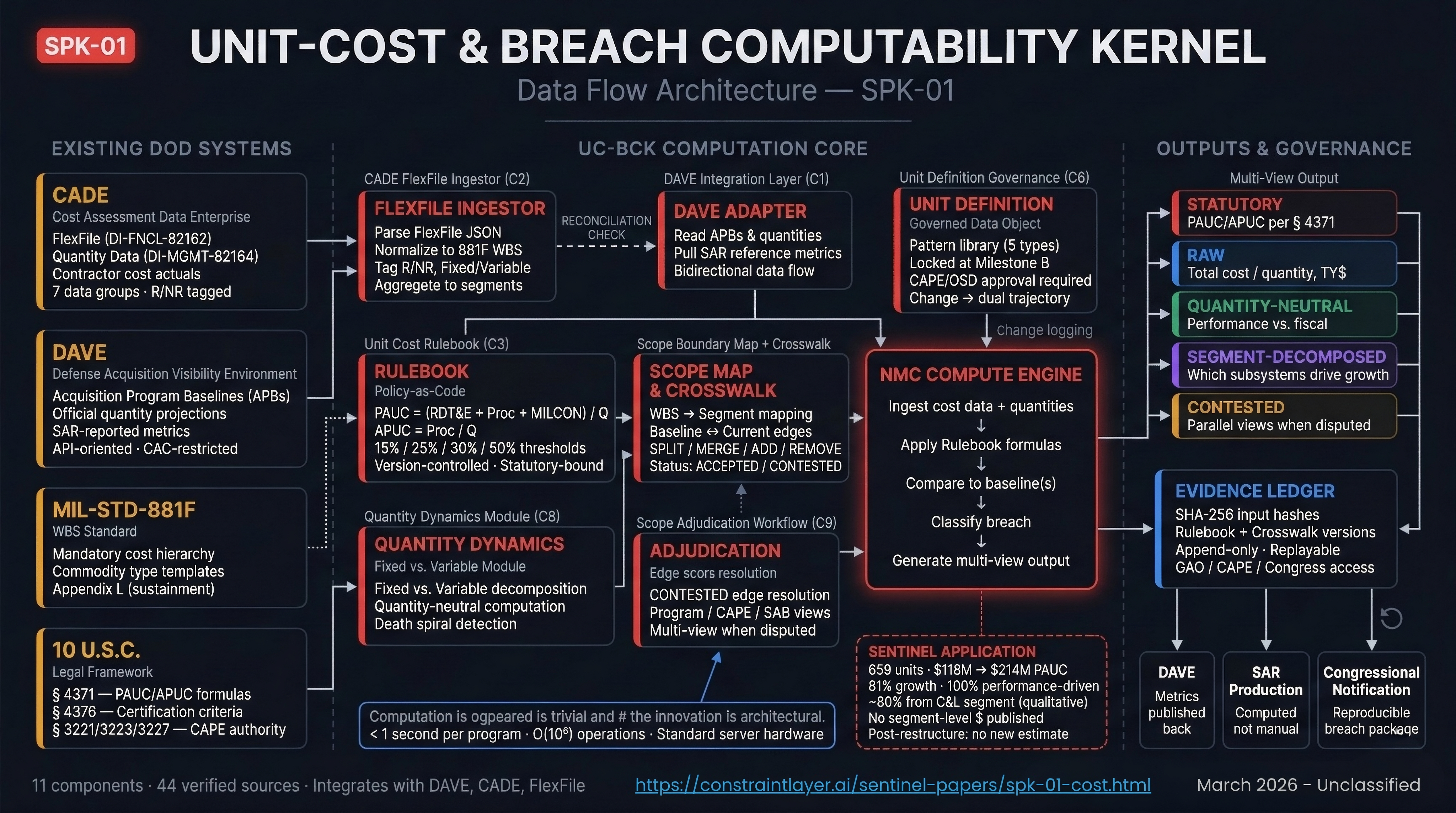
UC-BCK is a governance and technical architecture closing the three gaps. It integrates existing systems (DAVE, CADE, FlexFile) with three new capabilities: a locked, machine-readable unit definition; a reproducible computation engine; and a multi-view evidence ledger.
| Component | Purpose | Input/Output |
|---|---|---|
| Unit Definition Governance | Lock unit definition at milestone; govern changes; machine-readable format | In: Scope document / Out: Approved definition + version history |
| Baseline Crosswalk | Map original to current baseline; document every adjustment | In: Baseline snapshots / Out: Structured crosswalk with audit trail |
| FlexFile Ingester | Parse contractor cost data from CADE; validate schema | In: FlexFile JSON / Out: Normalized cost vector |
| NMC Compute Engine | Calculate PAUC and APUC from first principles | In: Cost vector, definition, baseline / Out: Metrics + variance |
| Threshold Alert | Continuous monitoring; alert approaching or exceeding breach | In: Computed metrics / Out: Alert with severity and margin |
| Evidence Ledger | Immutable log of submissions, computations, determinations | In: All data / Out: Timestamped, signed entries |
| Multi-View Generator | Produce statutory, raw, quantity-neutral, segment-decomposed, contested views | In: Computation result / Out: Five parallel views |
| Adjustment Rulebook | Policy-as-code: permissible, governed, and prohibited adjustments | In: Proposed adjustment / Out: Approval or rejection + reasoning |
| Contested Mapping Router | Route disagreements to independent arbitration; produce both views | In: Contested element / Out: Parallel computations |
| Segment Decomposer | Break PAUC growth into drivers: quantity change, per-unit cost by segment | In: Full cost data / Out: Attribution table by segment |
| GAO Replay Module | Export ledger + rules as auditable package for independent verification | In: Ledger + engine / Out: Reproducible audit package |
| View | Description | Purpose |
|---|---|---|
| Statutory | PAUC/APUC per 10 USC § 4371, with approved adjustments | Official Nunn-McCurdy determination |
| Raw | Total cost / total quantity, no adjustments, Then-Year dollars | Budgetary reality visible to Congress |
| Quantity-Neutral | Growth holding quantity at baseline, Base-Year dollars | Isolates performance-driven growth |
| Segment-Decomposed | Growth contribution by program segment | Identifies which subsystems drive growth |
| Contested | Parallel computation under contractor vs. government assumptions | Surfaces disputes explicitly |
If quantity had been reduced (as in F-22 or DDG-1000), these views would diverge—and that divergence is precisely the information Congress needs.
| Phase | Timeline | Deliverables |
|---|---|---|
| 1. Foundation | Months 1–6 | Standards authority; unit definition schema; adjustment rulebook; multi-stakeholder board |
| 2. Pilot | Months 7–18 | NMC Compute Engine; Crosswalk DB; DAVE/CADE integration; Sentinel pilot validation |
| 3. Rollout | Months 19–36 | All MDAP baselines migrated; FlexFile mandate; quarterly UC-BCK reports |
| 4. Lock-In | Months 37–60 | Embed in § 4371;[5] update § 4376[8] to require UC-BCK; GAO replay access |
All components are TRL 9. DLA's ASSR system demonstrates the approach within DoD: 98% manual work reduction on the Pega platform, processing 250,000–300,000 transactions annually.[35] DAVE is already API-oriented.[11] DFARS 234.71 already requires audit trails.[27] Computation completes in under 1 second per program.
Organizational (HIGH): Program managers will resist transparency. Mitigation: pilot with Sentinel post-restructure, where the Air Force has committed to transparency.
Technical (LOW): All proven technology. Mitigation: iterative pilot approach.
Political (MEDIUM): Contractor lobbying against mandates. Mitigation: frame as transparency tool benefiting all parties.
Congress: Earlier breach detection. Independent verification. GAO: Automated replay; reduced audit cost.[36] Program Managers: Early warning; defensible reporting. Contractors: Clearer unit definitions; formal appeal mechanism. Researchers: Standardized, reproducible cost data for independent analysis.
UC-BCK closes three gaps that have persisted for four decades. It produces a cost accounting architecture that is reproducible (any party can verify any breach determination), auditable (every figure has a source and trail), contestable (disagreements routed through governance, not suppressed), and early-warning (continuous monitoring before breach thresholds). It requires legislative updates aligned with the FY 2006 NDAA framework[6] but no new authorities or systems. Achievable within 5 years.
Cost growth and schedule slippage are coupled. When schedule slips, fixed costs accumulate, driving PAUC growth. SI-CK identifies schedule violations whose cost consequences flow into UC-BCK's segment decomposition.
Approximately 80% of Sentinel's cost growth originated in the Command & Launch segment. The construction constraints documented in SPK-03 are the physical root cause of the cost growth that UC-BCK measures.
NC3 interface complexity drives cost growth within the Command & Launch segment. The interface epochs and concurrent operation challenges SPK-04 maps are drivers of the cost growth UC-BCK measures.
Cost growth from network hardening, digital component validation, or security re-design flows into UC-BCK. SPK-05 documents cyber-surety as a constraint-closure mechanism with joint rules matrices.
Every inadequate test cell has a price tag. Additional W87-0 delta testing, PSSTF construction costs, and nuclear-certified software analysis are cost elements traceable through UC-BCK's segment decomposition.
WST-K identifies sustainment investments—propellant recapitalization, NS-50 guidance replacement, PSSTF construction, software workforce expansion—that UC-BCK must fund as distinct cost elements.
UC-BCK must satisfy eight acceptance criteria to close the identified gaps. All remain unmet.