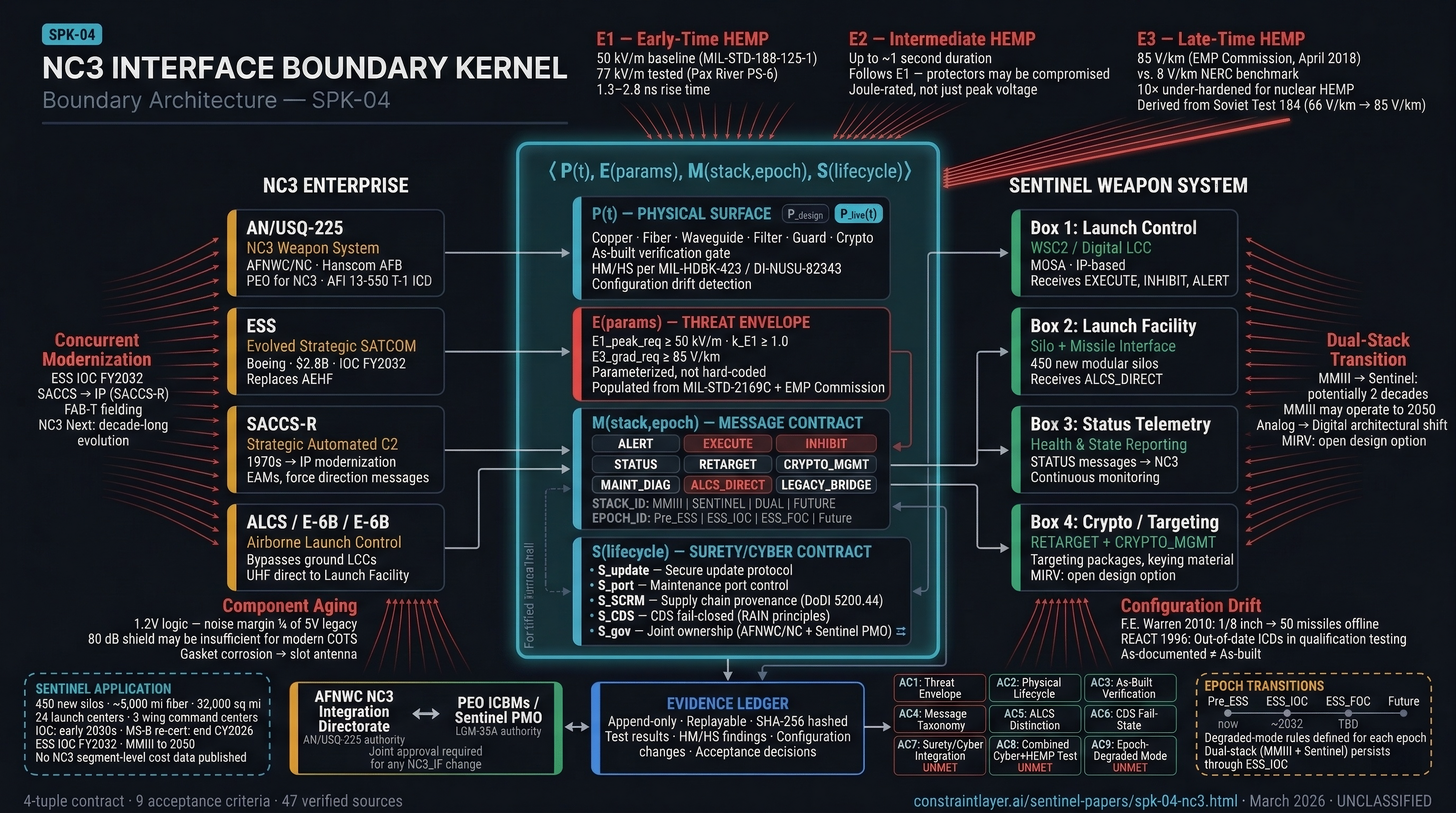
The interface where presidential authority flows to the weapon system and operational status returns to national leadership is the most consequential boundary in defense acquisition. Sentinel must integrate into an NC3 enterprise that is itself transforming — new satellites, new networks, new threats — while maintaining nuclear surety through a multi-decade dual-stack transition with Minuteman III. The EMP Commission recommends hardening to 85 V/km — an order of magnitude beyond commercial standards. NC3-IBK defines and validates this boundary.
Sentinel is the first U.S. strategic nuclear system designed for a digital, networked environment. Minuteman III uses point-to-point analog wiring and hardware logic. Sentinel uses IP-based communications, software-defined processing, and a Modular Open Systems Architecture. This is not an upgrade — it is an architectural transformation.
The 2024 Nunn-McCurdy breach documented "ineffective systems engineering" and "incomplete basic system design" as root causes.[1] While cost growth concentrated in ground infrastructure (~80% from the command and launch segment), the breach revealed that NC3 integration planning was designed against assumptions that no longer hold.
No validated Integrated Master Schedule for NC3 integration exists.[22] The AN/USQ-225 NC3 Weapon System has mandatory interface control documentation (T-1 requirement), but the substance of those interfaces — what must be specified, verified, and maintained — lacks computational structure.[23]
Three documented incidents validate the need for rigorous NC3 interface specification.
50 Minuteman III missiles dropped offline — one-ninth of the active U.S. ICBM arsenal. Command authority was severed. The root cause: a single replacement circuit card seated one-eighth of an inch from fully seated. This caused a Launch Control Center to transmit data in the wrong time slot, desynchronizing the multiplexed communication network.[27]
DoD IG Report 96-073 documented that the REACT program used out-of-date Interface Control Documents during qualification testing. The IG recommended higher priority for maintaining current ICDs. The principle: "as-documented" is a hypothesis — only "as-built" reality matters.[25]
GAO/NSIAD-93-181 found the Minuteman III Guidance Replacement Program planned to proceed to EMD before degradation was "adequately justified." The flight reliability impact of wet slug tantalum capacitor dry-out was unknown — yet the program moved forward. The pattern of committing to architectural changes without verified interface baselines recurred in Sentinel's 2020 baseline.[29]
The electromagnetic threat has evolved beyond the assumptions underlying foundational hardening standards.
MIL-STD-188-125-1 establishes 50 kV/m as the unclassified E1 baseline with 80 dB shielding (20 MHz–1 GHz). But the Pax River PS-6 pulser tests to 77 kV/m because assessed threats exceed legacy assumptions.[30][33]
Between E1 and the late-time E3, the intermediate E2 component (lasting up to one second) resembles lightning-induced transients — but arrives after E1 may have already damaged the protective devices designed to stop it.
| Parameter | NERC TPL-007 | EMP Commission |
|---|---|---|
| Source Event | Solar Geomagnetic Disturbance | Nuclear Detonation (MHD) |
| Field Strength | ~8 V/km | 85 V/km |
| Affected Area | High latitudes primarily | Entire CONUS |
| Rise Time | Minutes to hours | Seconds |
Sources: NERC TPL-007; EMP Commission, April 2018.
The 85 V/km figure derives from Soviet Test 184 (K-Project, Kazakhstan, 1962), which measured 66 V/km at ground level. The Commission scaled this to CONUS latitudes where E3 fields are stronger due to geomagnetic orientation.[3][5]
MIL-STD-188-125-1 was derived for 5V/12V electronics. Modern COTS at 1.2V have noise margins approximately one-quarter as large. The 80 dB shield may be insufficient for contemporary components even if the facility met specifications designed for legacy electronics.
Three regulatory changes transform the NC3 interface landscape.
Reissued December 17, 2024, the Fourth Surety Standard now reads: "prevent unauthorized access or unauthorized acts by physical or digital means." The phrase "by physical or digital means" is new — elevating cybersecurity from generic IT compliance to a Nuclear Surety Standard requiring the same rigor as physical custody and two-person control.[8] At the interface level, this is why critical commands cannot use simple DC voltage levels — an EMP event or short circuit could simulate a logic "high," potentially mimicking a launch signal.[39]
DoDI 5200.44 mandates SCRM for mission-critical functions, explicitly naming integrated circuits, FPGAs, and printed circuit boards. Hardware trojans are a surety threat.[9]
The NCDSMO under NSA mandates RAIN principles for Cross Domain Solutions: Redundant, Always Invoked, Independent, Non-bypassable. For NC3 interfaces, CDS devices must satisfy RAIN and survive HEMP without rebooting into an "open" state.[10]
The NC3 enterprise operates through two layers.[12]
Layer 1 — Day-to-Day ("Thick Line"): Commercial satellites, standard military networks, the modernized SACCS network. Efficient for force management. Not expected to survive full-scale nuclear attack.
Layer 2 — Survivable ("Thin Line"): AEHF/ESS satellites with protected waveforms, VLF/LF radio, airborne nodes (E-4B, E-6B Mercury). The enduring core.
The E-6B Mercury's Airborne Launch Control System (ALCS) provides direct launch capability for ICBMs, bypassing ground-based Launch Control Centers entirely. This creates a secondary, wireless attack surface on the silo distinct from hardwired intersite cables. NC3_IF_BOUNDARY_SPEC must distinguish ground-initiated from airborne-initiated commands.[34]
| Program | Function | IOC | Sentinel Role |
|---|---|---|---|
| LGM-35A Sentinel | Land-based deterrent | Early 2030s | Primary weapon system |
| ESS | Evolved Strategic SATCOM | FY2032 | Future protected comms |
| SACCS-R | Terrestrial C2 network | Ongoing | IP-based LCC connectivity |
| FAB-T | Satellite terminals for LCC | Fielding | AEHF/ESS ground link |
Sources: SSC, Breaking Defense.
The AFNWC NC3 Integration Directorate at Hanscom AFB serves as PEO for the AN/USQ-225. AFI 13-550 establishes interface control documentation as T-1 mandatory.[23][24]
NC3-IBK treats the NC3/weapon-system boundary as a single, formally structured interface contract:
Every penetration of the hardened boundary — copper, fiber, waveguide, filter, guard, crypto module — exists in three states:
P_design — the intended set. P_as_built — verified by inspection and EM testing. P_live(t) — the effective set at time t, accounting for repairs, degradation, and unauthorized changes.
NC3_IF is not accepted until P_as_built matches P_design. Hardness Maintenance/Surveillance per MIL-HDBK-423 and DI-NUSU-82343 tracks degradation over the lifecycle.[6][7]
A 2007 survey by the Institute of the North and Claremont Institute found that 96% of state Adjutants General indicated significant concern over an EMP attack, yet the majority had done "little or no analysis" of the impact on potential targets in their state. None were actively involved in a formal EMP planning process.[38]
Real-world maintenance patterns reveal gaskets oxidizing and deforming, personnel creating penetrations without installing required waveguides, and filter grounds corroding. A single compromised gasket can degrade a shielded door's effectiveness, allowing EMP energy to couple into the facility. P(t) exists because hardening degrades — and without lifecycle tracking, the degradation is invisible until failure.
Rather than hard-coding threat values that become obsolete, NC3-IBK exposes parameters: E1_peak_req ≥ 50 kV/m, k_E1 margin factor ≥ 1.0, E3_grad_req ≥ 85 V/km. Classified values from MIL-STD-2169C populate the parameters; the structure remains unclassified.
Nine message families crossing the boundary, each tagged with STACK_ID (MMIII, SENTINEL, DUAL, FUTURE) and EPOCH_ID (Pre_ESS, ESS_IOC, ESS_FOC, Future):
Five mechanisms integrated at the boundary:
S_update: Secure update protocol — multi-person authentication, regression testing against surety and HEMP baselines before returning to operational mode.
S_port: Maintenance port control — physically lockable, logically disabled in normal modes. GAO-19-128 documented that red teams took control of weapon systems "relatively easily" via maintenance laptop vectors.[43]
S_SCRM: Supply chain provenance verification for all NC3_IF-critical components per DoDI 5200.44.[9]
S_CDS: Cross Domain Solutions must follow RAIN principles and fail to closed/safe under HEMP, internal faults, and combined cyber+EM stress.
S_gov: Joint ownership — AFNWC NC3 Integration Directorate + Sentinel Program Office. Any change requires dual approval.
1,000 acres west of Ogden, Utah. The primary Air Force lab for ICBM nuclear hardness. Actively upgrading: new 50,000 sq ft radiation facility with Advanced Radiation Environment Simulator, Small Flash X-Ray, and 14-MeV neutron generator. Boeing $405M contract for testing in "extreme environments."[45][46]
The PS-6 pulser — a 125-meter outdoor system for whole-aircraft HEMP illumination. Peak fields of 77 kV/m at 24.5m, rise times 1.3–2.8 ns. System-level testing aligned with MIL-STD-464.[33]
AC8 requires at least one test combining EM stress with cyber penetration. The infrastructure exists today: configure representative NC3_IF equipment in a shielded chamber, apply EM stress (RS105, PCI, E3 injection), run concurrent red-team cyber attempts, and monitor for unauthorized command acceptance, boundary compromise, and CDS fail-state behavior. This is procedural integration, not new infrastructure.
Milestone B re-certification is expected by end of calendar year 2026. NC3-IBK must be established before the new baseline is approved. Once a baseline is set without NC3-IBK conformance requirements, the opportunity closes until synchronization failures or survivability gaps force another breach review.
NC3-IBK requires no statutory changes, no new technology, and no research-grade algorithms. All components are TRL 9. Implementation is a specification, governance, and testing discipline problem — not a technology problem.
NC3-IBK defines nine testable pass/fail conditions. All remain unmet as of March 2026.
NC3 hardening, testing, and HM/HS have associated costs tracked through UC-BCK. Public sources do not decompose NC3-specific costs within the command and launch segment.
NC3-IBK states map to schedule indices. Missile design freeze precedes physical acceptance, which precedes integration test, which precedes wing IOC.
NC3_IF requires completed ground infrastructure — cable corridors, LCC facilities, power systems. The ~5,000-mile fiber network faces the same seasonal constraints GI-PCK documents.
SPK-04 defines the boundary contract. SPK-05 defines the joint rules governing what crosses it. Any NC3 digital component entering a surety-controlled volume must clear SPK-05 rules.
AC8's combined cyber+HEMP test integrates with the overall test campaign. LMTF upgrades directly support Sentinel NC3 interface verification.
NC3_IF work requires TS/SCI clearances (~249 days). Nuclear-critical software requires NSCCA-credentialed personnel. The clearance pipeline constrains NC3-IBK execution.